Recently I was dispatched to Lille to attend the 8th International Cybersecurity Forum to report live, and shortly after I shared some key insights from the top keynotes focusing on the political agenda around cyber-security, including copies of keynote speeches at the event from European Commissioner Günther H. Oettinger, French Interior Minister Bernard Cazeneuve, and Security Minister at the UK Home Office John Hayes.
[easy-tweet tweet=”Take #DataSecurity out to sea with @BillMew’s interview with Patrick Hebrard from the #DCNS group” user=”comparethecloud”]
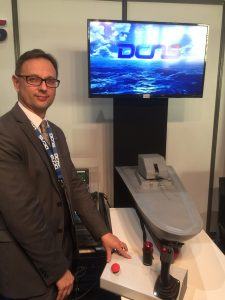
In addition to interviewing France’s top Cyber-cop (Francois-Xavier Masson, Chef de l’ OCLCTIC) and its top Cyber-regulator Guillaume Poupard (general manager of ANSSI), I also spoke to naval cyber-security expert Patrick Hebrard from DCNS Group.
Combating modern cyber threats to naval systems
IT managers everywhere are having to deal with the increasing volume and sophistication of cyber-threats – both those that are external and deliberate such as hacks and data thefts, and those that are down to incompetence such as data loss or lack of encryption. Modern warships are just like floating data centres with a combination of PC-based systems, Unix systems and more bespoke weapons systems. The only difference in the context of a naval warship is that once it leaves harbour the data centre is truly off the grid. One might think that having no direct link to the outside world might ensure complete security, but vulnerabilities still exist.
IT managers everywhere are having to deal with the increasing volume and sophistication of cyber-threats
Just as hackers are able to hack corporate data systems, it’s possible for a small group or a state with the right skills to hack the systems of an enemy ship, to steal data, to take control of the ship, of its information system, of its weapon system or one of the many monitoring and control systems used for managing the ship’s mechanical systems from its power generation and supply to its propulsion and steering.
There are external threats that could come from a developer who has deliberately, malevolently or even accidentally introduced malware into a system or an item of equipment. Then there are threats from simple negligence and ill-informed use of compromised equipment by maintenance engineers or use of infected devices, CDs or USB keys by members of the crew.
[easy-tweet tweet=”Just as #hackers are able to hack corporate #datasystems, it’s possible to hack the systems of an enemy ship”]
While common sense and discipline among maintenance staff and crew is the first line of defence, Hebrard suggests that this kind of static protection in no longer enough and that dynamic protection through detection, responsive-systems, counter-measures is now best practice just as it would be to more physical threats such as a missile attack.
When an incident occurs and the detection of cyber-signals or other signs of cyber-attack triggers the counter-measures there may be limited cyber-skills on board so teams work in collaboration with shore-based operational security centres.
The human factor is addressed through best practices in cyber hygiene, in accordance, in line with the rules defined by of the national information system security agency (ANSSI). ANSSI also runs a national accreditation and certification program that all systems need to pass before being adopted for use on board French warships.
Integrating the various systems and minimising the cyber-threat is then down to specialists like DCNS
Integrating the various systems and minimising the cyber-threat is then down to specialists like DCNS. It believes in ‘Security by Design’ from conception to deployment, including both warranty and maintenance phases.
The unfortunately reality is that sailors have been picking up nasty viruses in foreign ports of call for hundreds of years. The difference now is that the greatest threat might well come from a virus on a discarded USB key or infected mobile phone. As ever discipline among the crew and dockyard staff is crucial, as is the protection afforded by experts such as DCNS.
Bill is a tech industry veteran and experienced corporate marketing and communications professional with over 20 years spent working in blue chip organisations mostly in pan-European and global communications roles. He is also a regular commentator on #Cloud, #SocialSelling and #InfluencerMarketing, as well as a dad with a passion for technology, economics, politics & Arsenal FC.




Comments are closed.