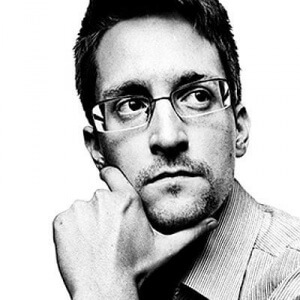
In 2013 when Edward Snowden, the former CIA employee and former government contractor, leaked classified information from the United States National Security Agency (NSA) he set off a chain of events that have yet to subside.
The slow burning fuse that he lit caused a major explosion last week with more predicted to follow. Safe Harbour, the legal framework for data transfers based on an agreement in 2000 between the European Union (EU) and the US, has been struck down in the European courts.
Ever since the Snowden leaks it has been increasingly evident to most in the industry that the surveillance he unveiled and the data privacy regulations in the EU were mutually incompatible, and that it was therefore just a matter of time before Safe Harbour fell. Having seen the end of the Safe Harbour agreement coming for a while now, all the major cloud players had already taken steps to prepare for last week’s ruling. The large firms, with a few exceptions, almost all now have data centres within the EU, and privacy and data management policies in place that adhere to local regulatory requirements.
[easy-tweet tweet=”The Snowden chain reaction is ringing out through Europe with #safeharbour being struck down” user=”billmew” usehashtags=”no”]
Smaller companies that lack the financial and legal means to get around the ruling as easily will be impacted more by the ruling. Most of the firms that relied on Safe Harbour simply don’t have the resources – unlike Facebook, Google and Microsoft – to create alternative corporate legal structures for their transfers of data. They will therefore be left in limbo until each country rules on the Safe Harbour agreement.

For those with adequate resources, there are of course are still mechanisms that companies can use to transfer data, including binding corporate rules and a presence in the EU to keep and store sensitive data.
Predicting exactly how each country will respond to the Safe Harbour ruling is almost impossible. At a recent briefing at IPExpo, Jimmy Wales, founder of Wikipedia expressed the concern that: “We may be moving to a balkanised era, where data has to be held in a country very specifically across many different jurisdictions.” This balkanisation could lead to the creation of multiple country-specific Internets, each gated off legally and governed by its own privacy laws, impacting the ability to provide harmonised services across borders.
In the longer run though, Wales believes that while data sovereignty will remain an issue, the focus will move from location to tokenisation and encryption – as tokenisation allows the data to remain in its country of origin and as all data becomes encrypted. This brings us to the next domino that is about to fall – cryptography.
the next domino is about to fall – cryptography
Most public key crypto-systems currently in use are built on integer factoring and discrete logarithms (such as RSA and ECC). The problem is that there is a quantum algorithm (Shor’s algorithm) that already exists, which, given enough computing power, can break them. And with the development of quantum computers there could soon be systems capable of capitalising on Shor’s algorithm to break these public key crypto-systems.
Conversely there are symmetric key ciphers such as AES that are considered quantum-safe and will play an important role the post-quantum world of next generation cryptography.
So what does this all mean for you?
Each European Union company will need to designate a single person as data controller. This data controller will need to follow exactly how each country responds to the Safe Harbour ruling and to ensure that you comply with each regulatory requirement.
[easy-tweet tweet=”The #SafeHarbour agreement never provided any real protection for your #data” user=”billmew @comparethecloud” usehashtags=”no”]
However it doesn’t really matter what protective measures or agreements this person puts in place (the Safe Harbour agreement never provided any real protection), if there is a breach then you are fully liable.
In addition to tokenisation to allow data to remain in its country of origin, your best bet is to ensure that all your data is effectively encrypted, but most current encryption will soon be rendered ineffective.
If you are implementing a crypto system now then you need to be sure that it will protect the data for its entire lifecycle (and for things like patient data, this can literally be a lifetime). Indeed for all of your data you need to be planning now for the transition to the use of quantum resistant algorithms or quantum key distribution, or ideally both.
You have been warned.
Bill is a tech industry veteran and experienced corporate marketing and communications professional with over 20 years spent working in blue chip organisations mostly in pan-European and global communications roles. He is also a regular commentator on #Cloud, #SocialSelling and #InfluencerMarketing, as well as a dad with a passion for technology, economics, politics & Arsenal FC.



