The future of online security is in the hands of Artificial Intelligence (AI); that’s the prediction many industry experts are currently making. Although the development of computers capable of intelligent thought is nothing new, AI experts are now starting to expand the capabilities of their technology.
[easy-tweet tweet=”The future of online #security is in the hands of AI; that’s what industry experts are predicting”]
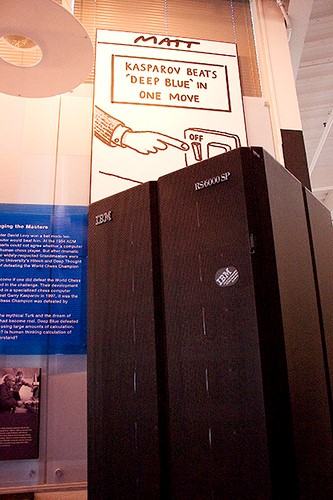
Indeed, back in the 1950s breakthroughs such as alpha-beta pruning were hugely important, but mainly because they allowed computers to play chess at a more advanced level. While it’s true that chess has been one of the benchmarks for the capabilities of AI machines over the years, developers have moved on to new pastures ever since Deep Blue beat Garry Kasparov in 1996.
AI’s Gaming Skills Could Provide Smart Security Solutions
“Deep Blue” (CC BY 2.0) by James the photographer
Today, researchers such as those at Carnegie Mellon University are working to solve games such as No Limit Texas Hold’em. Unlike chess where all the variables are known (each player knows the spectrum of possible moves in any situation), No Limit Texas Hold’em is a game of unknown variables.
Because the betting is unrestricted and a player’s cards aren’t on display, the number of possible hand combinations and moves makes it almost impossible to predict what’s going to happen. For AI researchers this poses a tantalising opportunity to develop the abilities of AI machines and in 2015 Claudico took on some of the best players in the world.
Developed by Tuomas W. Sandholm and his team at Carnegie Mellon University, the AI program narrowly lost the match but proved that computers can now make optimal moves against unknown variables. In fact, it’s this result that’s promoted Sandholm to suggest AI could soon be used to tackle cybercrime.
Using the same level of analysis that allowed Claudico to play No Limit Hold’em, security systems of the future could detect the strategies of an opponent (i.e. a hacker) and then figure out a way to exploit the opponent’s weaknesses.
Modern Security is the Product of Evolution
“Cloud-computing (1)” (CC BY 2.0) by incredibleguy
While this technology may not be perfected for another decade, the roots are already there. If we look at the evolution of online security we can see a movement away from static systems towards programs that offer a more dynamic form of protection.
It used to be the case that small businesses would have to rely on stock security hardware to protect their systems. However, with small businesses now a target for hackers, something more is needed. This increased threat level has given rise to the use of cloud-based security solutions such as web application firewalls (WAFs) within the small business community.
[easy-tweet tweet=”WAFs offer a dynamic, cost-effective compliment to any business hardware” hashtags=”security, cloud”]
Offering a dynamic, cost-effective compliment to any hardware a business may own, cloud-based WAFs protects from common web application threats and vulnerabilities. From cross-site scripting to remote file inclusion and SQL injections, WAFs are currently the best way for businesses of all sizes to protect their data.
What’s more, this technology is both a product of the times and of the security industry’s evolution. Indeed, because cloud technology is now a mainstream product (rather than the niche projects like Salesforce.com were in 1999), industries are now able to tap into its capabilities and this is what the security industry has done over the last decade.
Instead of sticking to the hardware solutions of the past, leading security companies are now combining this technology with WAFs in order to provide multiple layers of protection. However, as with all things in the tech world, things will continue to evolve and that’s where AI could come into the mix. Whether it’s some form of standalone protection or the integration of AI with current solutions such as WAF, it looks as though that’s the way the industry is heading which, for consumers, should be seen as a positive.
Daniel Smyth has been a long time lover of tech and is most excited about the evolution of AI. Stemming from his love of games, in particular poker, Daniel is now charting the progress of programs such as Claudico and pondering the potential of these applications in fields such as security, medicine and beyond.